As you unbox your brand-new smartphone or laptop, you can’t help but feel excited to explore what it can do. Yet, the screen greets you not with a blank canvas but with a clutter of unfamiliar applications.
This seemingly harmless moment illustrates the pervasive challenge of pre-installed software colloquially known as “bloatware” also known as “junkware” or “crapware”, a phenomenon that extends beyond mere annoyance. In our digital age, where technology intertwines with every facet of life, bloatware presents almost no benefit while adding severe cybersecurity risks.
Understanding Bloatware

Why do manufacturers include bloatware in devices already brimming with features? The answer to this seemingly straightforward question is more intricate than meets the eye. Behind the scenes of sleek design and cutting-edge functionalities lies a complex interplay of factors that shape the bloatware landscape.
At its core, the driving force behind bloatware’s proliferation is a web of economic incentives for device manufacturers. With the competitive nature of the technology market, manufacturers often seek avenues to grow their revenue streams beyond the hardware sale itself.
One of those avenues is pre-installed software. By partnering with software developers, manufacturers can tap into additional revenue, allowing them to offer devices at more appealing price points. This symbiotic relationship, however, comes at a cost – the compromise of the user experience.
While additional revenue is the most powerful force behind bloatware it’s not the only one. Strategic alliances with software vendors also contribute to the equation.
Manufacturers often bundle their devices with software applications that serve niche needs or complement the device’s functionalities. While this collaboration can enhance the device’s appeal, it can inadvertently bloat the system, eroding performance and potentially introducing security vulnerabilities.
Types of Bloatware
Bloatware comes in various forms. Not all of them are equally useless or malicious, but every single one of them is hogging your device’s resources and diminishes the user experience.
Pre-installed Bloatware
This is software that comes already installed on a device by the manufacturer. It often includes applications that may not be essential to the device’s core functionality but are still included by default. Adds no value – takes up space.
Trialware or Demo Software
Sometimes, devices come with trial versions of software that offer limited features for a certain period. After the trial period ends, users are prompted to purchase the full version. You used it for a week and now it spams you with ads.
Manufacturer-Specific Apps
Device manufacturers may include their own apps and services on devices. While some of these apps can be useful, others might not align with your needs, leading to unnecessary clutter and resource usage. Baked in from the factory floor, usually non-removable.
Carrier-Specific Apps
Mobile carriers often install their apps on smartphones they sell. These apps might offer services related to the carrier but could also add to the bloatware load if they’re not relevant to you. Thanks, AT&T, but I don’t need them.
Bundled Software
Sometimes, software you want or need comes bundled with additional software that you don’t want. For example, when you install a free application on your computer, it might come with additional browser toolbars or other software that you didn’t request. Most of the time they let you opt out of those.
The Cyber Security Implications
Bloatware has gone beyond just being annoying, it also affects cybersecurity.
Weakening of System Security
Expanded Attack Surface: Bloatware’s main impact on cybersecurity is a larger “target area” for attacks. Each additional app that comes with your device or gets installed adds more places where attackers can try to get in. Your device is literally becoming a bigger and easier target!
Imagine your device as a castle – a solid structure with only a few entrances. You can put some guards on those entrances to control everyone who enters and exits. Now think of bloatware as a part of a castle that you didn’t build, to be honest, you have never even been there. It’s quite common for such “parts of a castle” to have hidden or simply unsecured backdoors.
That means that the more bloatware you have, the more opportunities there are for hackers to exploit your device.
Resource Consumption and Performance Impact: Bloatware’s stealing your device’s resources isn’t just a performance issue it is also a cybersecurity problem.
Bloatware running in the background is using up your device’s power, memory, and storage. This slowdown makes your smartphone or laptop work slower, apps take longer to respond, and tasks that are supposed to be quick are frustratingly sluggish.
This resource drain isn’t just about slowing down your device; it slows you too!
Think about a security alert – acting quickly can mean stopping a threat before it becomes a problem. But if your device is slow because of bloatware, you might not be able to respond fast enough. This delay creates a window of opportunity for cybercriminals who are good at exploiting these moments of weakness.
Privacy Concerns
Bloatware’s impact on privacy can be significant. This unwelcome software often engages in stealthy data collection, amassing insights about your digital behavior, preferences, and even more personal information.
What will they do with it? Most probably sell to a data broker. But who will buy this data later down the road? It may be marketers who want to send you more personalized ads, or it may be cyber criminals who want to use it in advanced phishing attacks. Either way, doesn’t sound good.
Even if the bloatware you have doesn’t snoop around your data, are you sure that it handles your data properly? That’s another layer of concern. When bloatware mishandles your data, it risks exposing your private information to unintended audiences, opening the door to identity theft, financial fraud, and a host of other privacy-related threats.
Vectors of Attack Through Bloatware
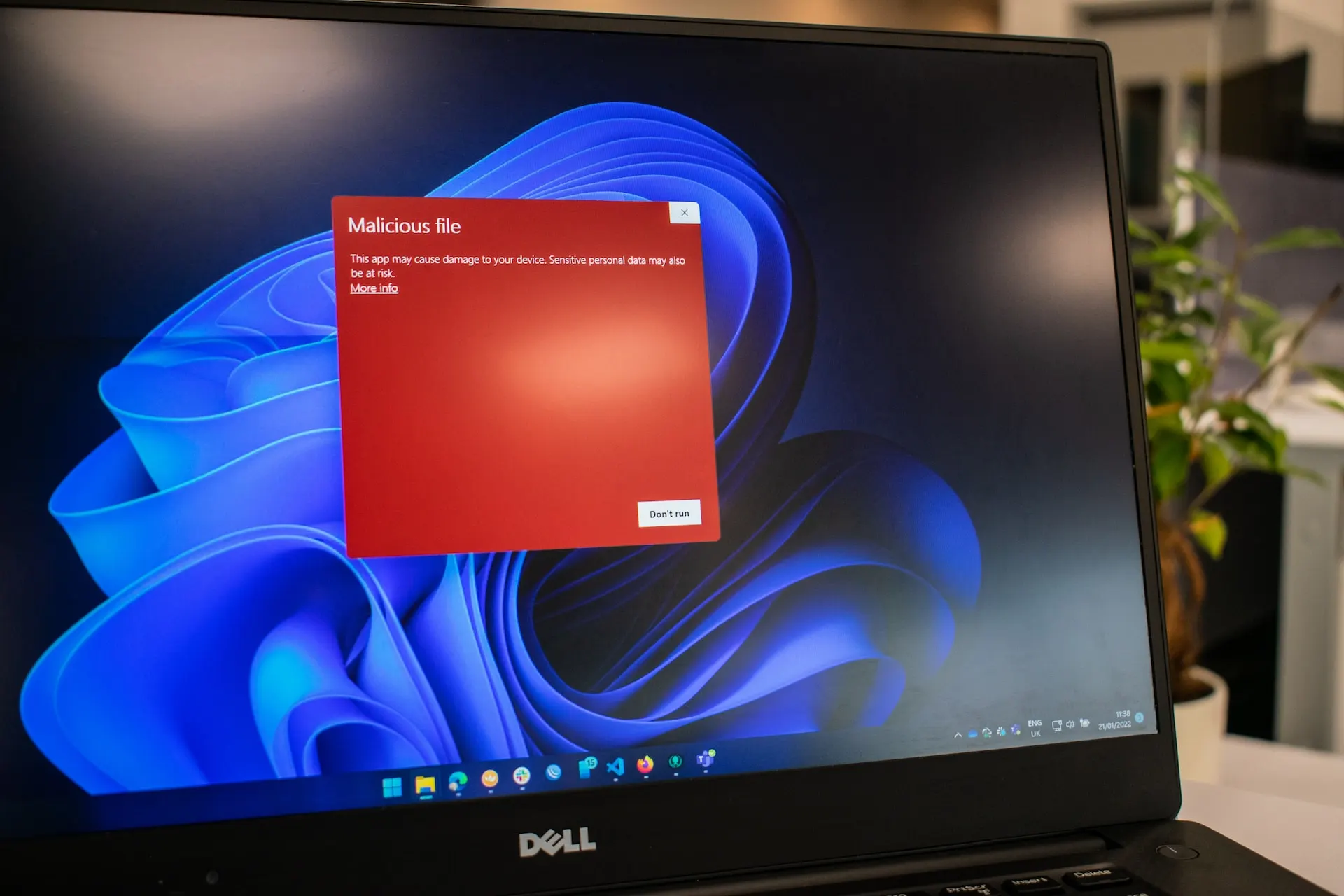
Malware Infiltration
Trojans, Adware, Spyware: Bloatware may unwittingly act as a Trojan horse, transporting various malware onto devices.
Real-world Example: In 2015, a malware-infected version of Xcode began circulating in China, and malware-ridden “XcodeGhost” apps made their way into Apple’s App Store and past the App Store review team.
There were more than 50 known infected iOS apps at the time, including major apps like WeChat, NetEase, and Didi Taxi, with up to 500 million iOS users potentially impacted. More than 100 million users were affected by the malware. The malware spread through altered copies of Apple’s Xcode development environment, and when iOS apps were compiled, third-party code was injected into those apps. Users downloaded infected apps from the iOS App Store.
Phishing and Social Engineering
Seemingly innocuous bloatware may be used for phishing attacks or to manipulate users into revealing confidential information.
Real-world Example: In 2016, a Chinese company called Adups was caught pre-installing spyware on millions of Android devices. The spyware was capable of collecting personal data and sending it back to Adups servers without the user’s knowledge. The company claimed that the spyware was installed by mistake and that it was meant to help Chinese phone manufacturers identify junk text messages and calls. However, the spyware was also capable of downloading and installing other apps without the user’s consent.
Update and Patch Neglect
The excessive presence of bloatware can obstruct the installation of critical security updates, rendering devices susceptible to known vulnerabilities.
Real-world Example: In 2017, the WannaCry ransomware attack affected more than 200,000 computers in 150 countries. The attack was caused by a vulnerability in Microsoft Windows operating systems that had been discovered by the US National Security Agency (NSA) and was subsequently leaked by a group called Shadow Brokers. The vulnerability was exploited by the WannaCry ransomware, which encrypted users’ files and demanded payment in Bitcoin to restore access. The attack was able to spread so quickly because many organizations had not updated their software to patch the vulnerability.
Poor Customer Data Handling
Some pre-installed bloatware apps may not implement robust security measures to protect user data. This can make them vulnerable to hacking and unauthorized access, putting users’ personal information at risk.
Real-world Example: In 2015, Lenovo was found to have pre-installed adware called Superfish on hundreds of thousands of laptops, compromising buyers’ security without warning. The software, developed by Superfish, Inc., delivered pop-up ads from the company’s retail partners whenever a user’s cursor hovered over a similar-looking product on a website. The software also scanned SSL-encrypted web traffic, creating serious security vulnerabilities.
Lenovo settled with US states for $3.5m and agreed to seek consumers’ consent before installing any such software in the future. Lenovo also settled a class-action lawsuit for $8.3m regarding the use of Superfish software in its laptops. They also provided a tool to manually remove the software from the infected devices.
An Actionable Plan to Tackle Bloatware
Step 1: Recognizing Bloatware
First things first, you need to spot bloatware on your devices. Here’s how:
- System Audit and Analysis: Conduct regular audits of your device, just like you’d do a tune-up for your car. It will help you to pinpoint and remove any lurking bloatware that has reinstalled itself or just survived previous culling.
- Suspicious Behaviors and Permissions: Look out for suspicious activity. Learn about behaviors like excessive permissions, unexpected pop-ups, or unrequested data access. This awareness will help you catch potential bloatware early and eliminate it.
Step 2: Your Removal Options
Now that you can identify bloatware, let’s take a look at how to get rid of it. Here’s how to safely remove it:
- Manual Uninstallation: Start by checking your settings. Most devices allow users to uninstall or disable certain pre-installed apps. Head to your device’s settings, find the app management section and remove all the unnecessary apps.If we are talking about PCs then you can use PowerShell or CMD: These are command-line tools that allow you to execute commands and scripts. You can use them to uninstall bloatware in bulk or to remove programs that are not listed in the Windows Settings. However, this method requires some technical knowledge and caution, as you may end up deleting something important or damaging your system.
- Third-Party Removal Tools: Try some bloatware removal tools. There are free and paid apps all over the internet, try some of them out.
- Factory reset: If you have any bloatware left, the next possible step is a factory reset. Since some bloatware, mobile carrier apps, for example, are installed on a device right before it gets sold, it is possible to reset the phone to a clean straight-from-a-factory state. Factory reset is hidden either somewhere deep in your settings or behind a weird combination of buttons. It may be different for every device, so you’ll have to Google it. Also, remember to back up your important data before taking this step.
- Jailbreaking/Rooting your device: After the factory reset, you have only 1 option left: Rooting/Jailbreaking. This is a last resort measure and only advanced users should use it. With careful rooting (Android) or jailbreaking (iOS), a user can gain full control over their devices. However, this process comes with potential risks of creating security vulnerabilities. And if you do try to root/jailbreak, you can kiss your warranty goodbye.
Step 3: Preventing Bloatware Installation
You’ve found and removed all the bloatware, now make sure that it doesn’t come back.
- Mindful Software Downloads and Installations: Take software downloads seriously. Be cautious about where you get the software and verify its authenticity. Being cautious with downloading software should prevent unwanted bloatware from making its way back onto your device.
- Custom Installation Options: Do not rush when installing software. Viciously clicking on “Agree” and “Continue” during installation will fill your device with useless browser extensions, adware, and other junk. Pay attention and make sure to remove checkmarks from stuff you don’t want.
Removing Bloatware is Hard but It Can Be Done
Removing bloatware can be complex because it is often pre-installed by the manufacturer or the retailer, and they intentionally make it difficult to remove. While getting rid of it might seem like an easy and straightforward idea, it’s not always true. Software can be tricky, especially when it is connected to other apps that may influence or depend on it.
Removing bloatware isn’t simple. By deleting files left and right, typing in PowerShell commands that you found on Google, and indiscriminately using third-party apps you might mess up your device, delete the wrong files, and lose your warranty. And even if you figure out how to do it on one device it doesn’t mean that you can do it on all other devices, using different devices and systems makes it impossible to find one solution that fits all.
That’s why we’re here. Our cybersecurity experts have years of experience dealing with bloatware and other cybersecurity issues. Don’t let challenges hold you back from improving your device’s security. Schedule a call with our cybersecurity experts today and take control of your IT health and safety.
Got bloatware under control? Feel free to contact us if you need professional help with any other IT issues.
- Is It a Microsoft Email or a Phishing Attack? - August 24, 2023
- Wired for Success: Building Secure Business Networks - August 16, 2023
- Client Confidentiality: Importance of Cybersecurity Services for Law Firms - July 31, 2023