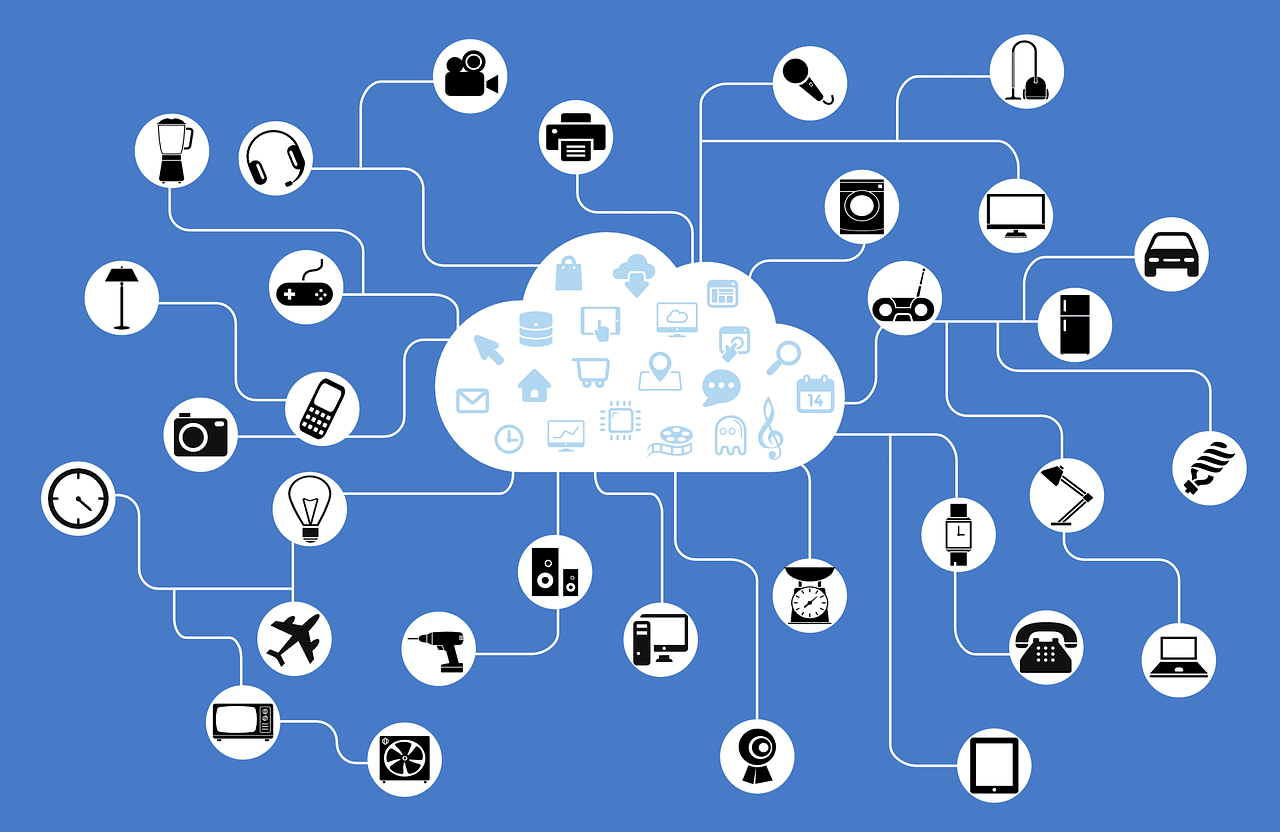
Over the last decade, the number of internet-connected devices in homes has been growing exponentially. A typical American home in 2020 had 10.37 devices connected to the internet. IoT devices make up a little over half of those and the rest are PCs and mobile devices.
IoT stands for Internet of Things, which means any type of “smart device” that connects online. IoT devices can be anything from your smartwatch to your refrigerator. Baby monitors and voice assistants like Alexa are also IoT.
Working remotely has become the norm for many businesses around the world. Home IoT devices are now sharing a Wi-Fi network with business devices and data, and it puts all IoT devices in danger.
Here are two alarming statistics on that issue :
- During the first two quarters of 2021, the number of IoT cyberattacks was up by 135% compared to the previous year.
- It’s estimated that ¼ of all cyberattacks against businesses involve breached IoT devices.
Hackers Can Use Your IoT Devices to Get to Your Computers & Smartphones
Smart devices can be a risk to any other device on the same network. They are typically easier to breach. That’s why hackers use them as a gateway into more sensitive devices.
When a criminal targets your IoT network they don’t care about the shopping list stored in your smart refrigerator or your jogging route recorded on your smartwatch. They breach IoT devices to see what other devices are connected to the same network.
The hackers can then use the device’s sharing permissions that are often present on home networks. Through them, hackers can gain access to your mobile device or work computer.
Why are IoT devices less secure? Here are a few reasons:
- They don’t have antivirus/antimalware capabilities
- Users rarely update their IoT devices
- They have basic interfaces which hide signs of a device breach
- People often don’t bother changing the default username and password
Put IoT devices on a Separate Wi-Fi Network
All modern routers have the ability to set up a secondary Wi-Fi network, called a “guest network.”
By putting all your IoT devices on a separate network you cut the bridge that hackers use to go from an IoT device to another device on the same network.
In fact, when you separate those two a hacker can’t even see if you have a PC or a smartphone connected to that network. This is because they’re on the other network.
This is an important additional layer of security you can use. Whether you’re a full-time remote worker or occasionally take your work laptop home for some extra work, it can help.
Here are the steps to separate your IoT devices. (Note, you can also have this done by us, we’ll be happy to help you out with your IT headaches.)
- Step 1: Go into your router settings.
- Step 2: Look for a settings area that allows you to set up a guest network. This can be different for each router model, so you may need to look around a little bit.
- Step 3: Set up the guest network according to the prompts given by the router. Make sure to use a strong password.
- Step 4: Change the password of your existing network. This will keep your IoT devices from automatically reconnecting back.
- Step 5: Connect all IoT devices in your home to the guest network you’ve just created.
- Step 6: Reconnect your PCs and smartphones to the preexisting network with the new password.
As you add new IoT devices to your home, make sure to connect them to the guest network. This will keep the layer of security effective.
One quick tip: When naming your Wi-Fi networks, don’t use descriptive names like name, address, or router model name. It’s best to avoid names that give the hackers valuable information they can use in attacks. Also, don’t name your networks “IoT network” and “Sensitive devices”, you are just pointing out to hackers which network is valuable and which one can be ignored.
Need Help Upgrading Your Cybersecurity?
With remote work becoming more popular, hackers have begun targeting home networks. They fish for personal and sensitive business data. Don’t leave yourself open to a breach, schedule a quick 10-15 minute talk about improving your cybersecurity!
You can trust EB Solution to do a great job, no matter how hard the task is! Our track record speaks for itself. We’ve been in this business since 2011, protecting our clients’ networks and databases 24/7, and never had a problem. We offer a wide range of cybersecurity services, including network security, password management, employee training, business continuity and data recovery.